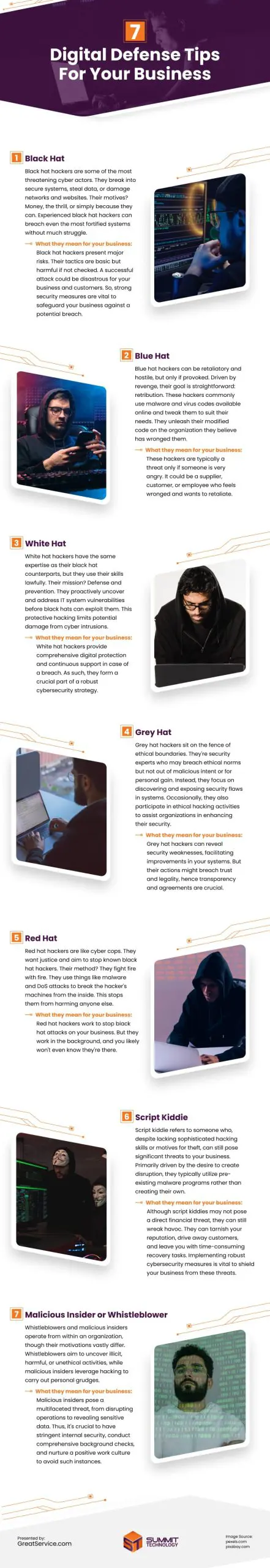
In today’s digital landscape, hackers come in various shades, from those who aim to bolster security to those who wreak havoc for personal gain. Understanding the spectrum of hackers is vital in fortifying your digital defenses.
Here are the different types of hackers and how to safeguard your company’s systems:
Black Hat Hackers
Black hat hackers pose significant threats in the cyber world. They infiltrate secure systems to steal data or cause harm to networks and websites. Their motivations range from financial gain to seeking excitement or merely testing their capabilities. These hackers can penetrate even the most fortified systems with ease.
Black hat hackers pose serious risks to your business. Their methods, though straightforward, can cause severe damage if not stopped. A successful attack could harm both your business and your customers. Therefore, robust security measures are crucial to prevent potential breaches.
Blue Hat Hackers
Blue hat hackers operate out of retaliation, using malware and virus codes to target organizations they perceive as adversaries. While they pose a threat when provoked, their actions are typically driven by personal grievances rather than financial gain.
White Hat Hackers
Unlike their black hat counterparts, white hat hackers utilize their skills for lawful purposes. They specialize in identifying and addressing system vulnerabilities to prevent cyber intrusions. Engaging white hat hackers can provide comprehensive digital protection and ongoing support, making them a valuable asset in cybersecurity strategy.
Grey Hat Hackers
Grey hat hackers operate in a gray area of ethics. While they may bend ethical norms, their intent isn’t malicious or for personal gain. Instead, they aim to uncover and disclose security flaws in systems. Sometimes, they engage in ethical hacking to help organizations enhance their security.
Grey hat hackers can find security problems in your systems, which helps make them better. But sometimes, people worry about whether their actions are trustworthy or legal. So, it’s important to be clear and agree on what they can do to help your business safely.
Red Hat Hackers
Red hat hackers act as cyber cops, seeking justice by stopping known black hat hackers. They combat malicious activities by using tactics like malware and DoS attacks to disable hackers’ machines. This prevents further harm to others. For your business, red hat hackers quietly work behind the scenes to thwart black hat attacks, often without your awareness of their presence.
Script Kiddies
Despite lacking advanced hacking skills, script kiddies can still pose significant threats by utilizing pre-existing malware programs. Their motive is often disruption rather than theft, employing methods like DDoS attacks to overwhelm systems. Implementing robust cybersecurity measures is crucial to mitigate the impact of script kiddie attacks.
Malicious Insider or Whistleblower
Operating from within organizations, malicious insiders and whistleblowers have distinct motivations. While whistleblowers aim to expose wrongdoing, malicious insiders leverage hacking for personal gain or vendettas. Stringent internal security measures, background checks, and a positive work culture are essential in mitigating these threats.
Hackers exploit security gaps for various reasons, making it imperative for businesses to prioritize cybersecurity measures. Implementing tools like antivirus software, unique passwords, and two-factor authentication can bolster defenses against cyber threats. Additionally, engaging managed IT support with a 24/7 security operations center can provide continuous monitoring and defense against evolving cyber threats. By understanding the hacker ecosystem and implementing proactive security measures, businesses can better protect their digital assets and mitigate potential risks.
source: https://www.greatservice.com/understanding-what-hackers-do-to-and-for-your-business/
Comments
Download this infographic.